WordPress 4.7.3 Security Release: You’ve Been Updated
WordPress 4.7.3 Security Release: You’ve Been Updated
Dear Adwebvertising clients and friends. Just a quick update. We have recently updated your WordPress site to address some vulnerabilities from previous releases. With our friends at WordFence your site has been secure and free of any worries brought on by these vulnerabilities.
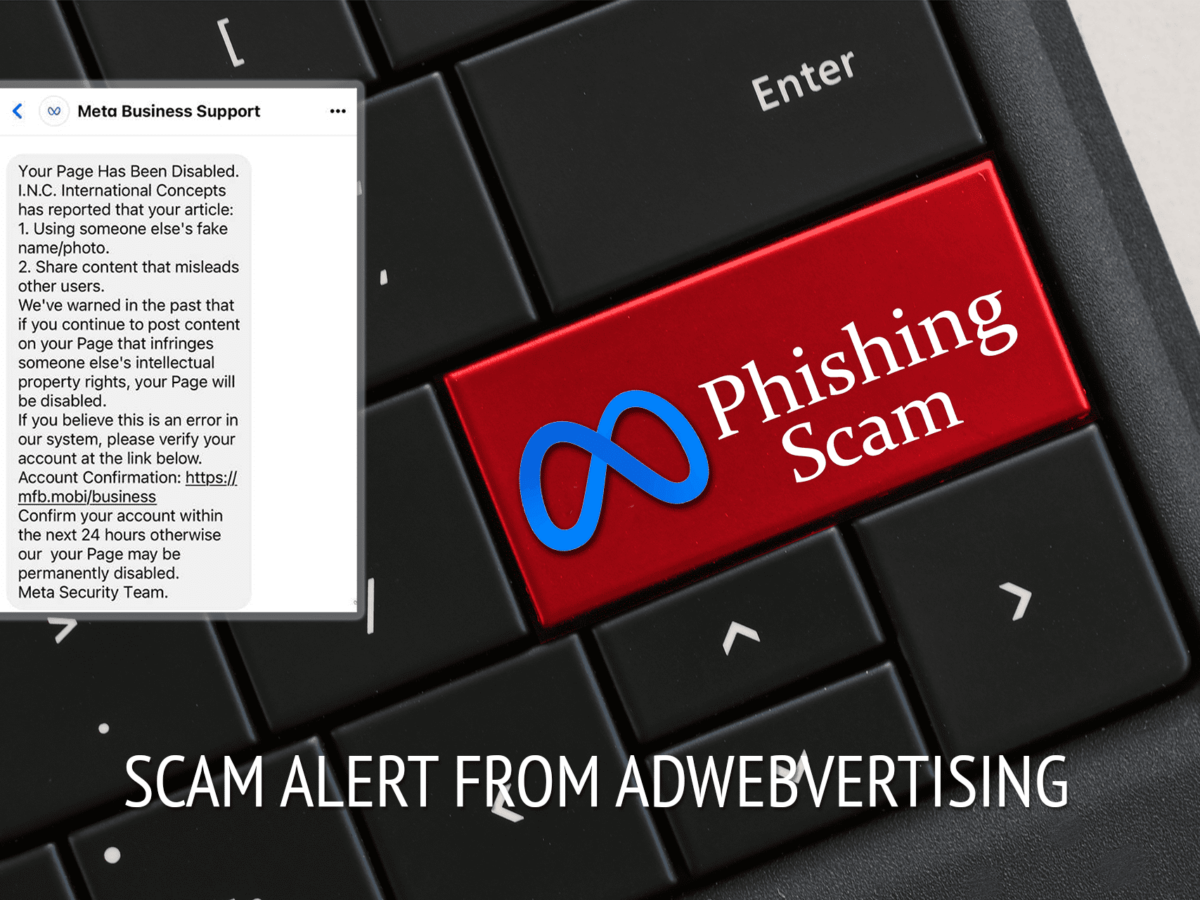
At Adwebvertising we take a great deal of concern when it comes to the safety of our clients sites and keep our finger on the pulse of things happening across the web so that your sites are always safe and secure.
The following is from our WordFence partners:
WordPress 4.7.3 has just been released. It is the third in a series of recent security releases for WordPress core.
WordPress 4.7.2 was released on January 26th to fix a now famous WordPress defacementvulnerability. WordPress 4.7.1 was released on January 11th which fixed a vulnerability in PHPMailer.
This new 4.7.3 core release fixes three Cross Site Scripting vulnerabilities:
- Cross-site scripting (XSS) via media file metadata.
- Cross-site scripting (XSS) via video URL in YouTube embeds.
- Cross-site scripting (XSS) via taxonomy term names.
It also fixed the following additional security issues:
- Control characters can trick redirect URL validation.
- Unintended files can be deleted by administrators using the plugin deletion functionality.
- Cross-site request forgery (CSRF) in “Press This” leading to excessive use of server resources.
WordPress 4.7.3 also contains 39 maintenance fixes to fix a range of non-security related issues.
A few minutes ago, the Department of Homeland Security released an upgrade advisory via US-CERT’s National Cyber Awareness System: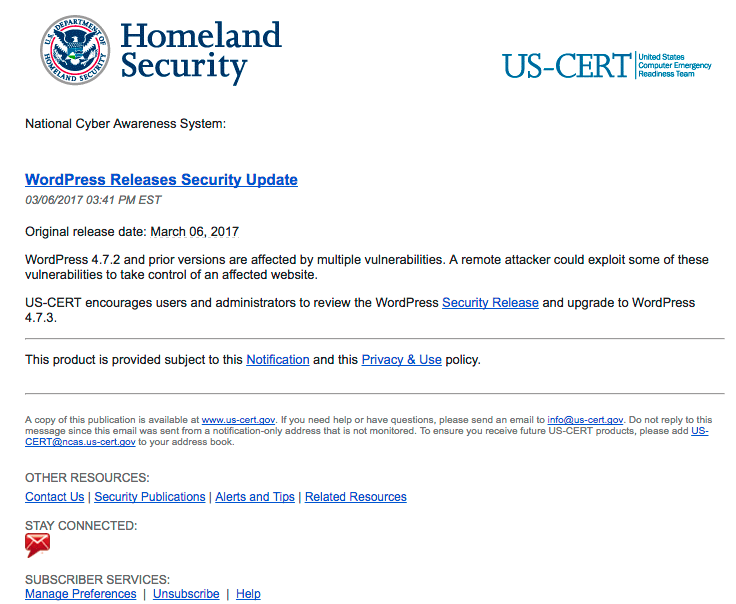
We would recommend that you don’t delay in upgrading to this new release. This release fixes multiple security vulnerabilities and now that the code changes are publicly visible, we may see attacks targeting these vulnerabilities emerge in the coming days.